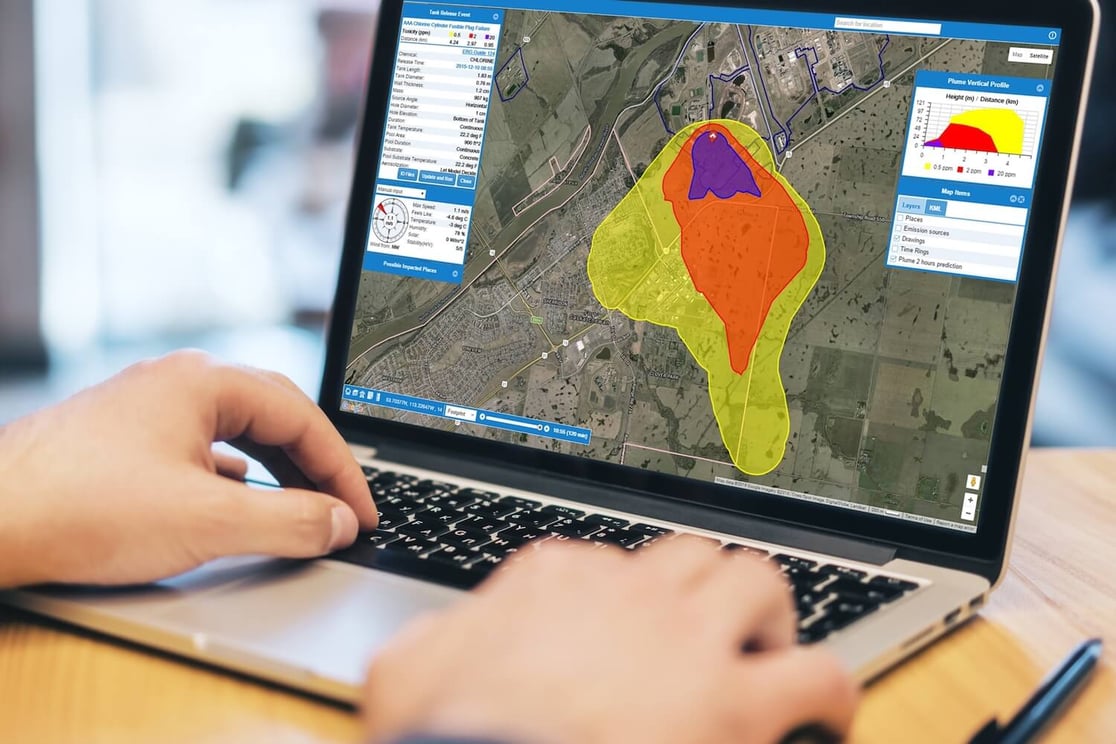
See Impacted Areas
Pinpoint danger zones on a map that combines real-time data from gas sensors, weather stations, and local traffic patterns.
Get real-time, predictive information to proactively respond to a chemical release and reduce the risk to your people, plant, and community with SAFER One Dynamic Plume Modeling Software.
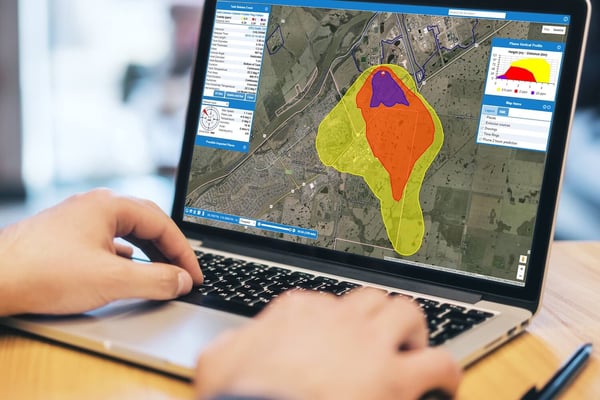

Access all the critical information you need to quickly identify the source, severity, and community impact of a chemical event. Integrate real-time data from on-site gas monitors, weather sensors, and Google Maps™ to make informed decisions about when, where, and how to respond.
See Impacted Areas
Pinpoint danger zones on a map that combines real-time data from gas sensors, weather stations, and local traffic patterns.
Stop Leaks Fast
Immediately identify the source of a chemical leak so you can stop it quickly.
Communicate Confidently
Effectively and accurately communicate your plans with first responders and stakeholders using detailed reports.
Eliminate Manual Processes
Improve efficiency by automating post-event analysis and odor-complaint processes.

Identify impacted areas using aggregate, real-time data from gas sensors, weather stations, and local maps.
Work faster by quickly identifying the source of a chemical leak and taking action to stop it.

Improve communication by sharing detailed, accurate reports with first responders and community stakeholders.

Eliminate tedious manual event analysis by automating it with our patented algorithm.
Simplify Emergency Response
Accurately predict chemical concentrations along the dispersion path to control the situation from start to finish.
Manage Odor Complaints
Stop odor complaints by quickly identifying any leak source at any time, even if it’s coming from somewhere else.
Prep Turnarounds and Shutdowns
Determine what could go wrong, then prepare your crew and emergency response team for these scenarios.
Get real-time analytics to improve safety, reduce risk, and manage productivity.
What is dynamic plume modeling?
Plume models are a vital tool you can use to plan for and manage a chemical release. Dynamic plume modeling tools incorporate real-time gas and weather data to give you accurate, up-to-date, and detailed information.
These tools generate an accurate plume model, then track and monitor all aspects of a chemical release from start to finish. With live data on the size, speed, and path of the hazard, you can see the impact in an instant—both on your site and within your community—and determine what actions you need to take to reduce risk. Whether it’s a chemical leak, derailment, or some other loss of containment, dynamic models have the power to immediately identify the problem.
Dynamic plume modeling software puts you in control by allowing you to monitor, model, and mitigate chemical releases.
Who should use dynamic plume modeling software?
Dynamic plume modeling software can be used in many industries and for many applications, including industrial plants, chemical storage facilities, pulp and paper mills, and emergency response scenarios.
Dynamic plume modeling makes the greatest impact in emergency response scenarios. During chemical emergencies, first responders often make critical decisions with little to no information. From fires to chemical spills, dynamic plume models can help emergency responders understand the impact on the community and make safe decisions about evacuation and shelter-in-place alerts.
How can I use dynamic plume models like SAFER One to be proactive?
You can use dynamic plume modeling tools like SAFER One to plan and prepare for future scenarios. For example, by collecting historical gas and weather data, you can explore if a plant-wide power outage would require you to flare product. If you had to do this, what gases would be released? Where would they disperse? When would you need to notify local authorities? Would you need to evacuate nearby homes? Would you need to close roads near your facility?
Asking these questions in advance allows you to develop an emergency response plan and be better prepared for an actual emergency.
How can SAFER One help me respond to chemical incidents faster?
Dynamic plume modeling software, like SAFER One, continuously monitors gas and weather sensors on your site so you can identify the source of a chemical incident as it’s happening—something static plume modeling tools cannot do. Whether it's a chemical leak, derailment, or some other loss of containment, dynamic models have the power to immediately identify the problem.
In the event of a chemical release, responders often face an "information gap" and must wait for answers. Knowing where the release occurred provides these answers, allowing responders to rapidly take decisive action to save valuable time and lives.
Can SAFER One improve emergency communication with my local community?
Yes! Dynamic plume models like SAFER One provide the facts your team needs to effectively communicate with community stakeholders.
As winds shift, so does the plume model, giving incident commanders and responders the most up-to-date information about the incident. Accurate predictions of the dispersion path, potential impact, and source of a chemical release allow you to communicate with confidence during an emergency.
Without this real-time information, you’re left using guesswork to predict where the plume might spread. You have to prepare emergency crews, workers, and the community for the worst-case scenario, which is not only less efficient, but also expends resources, increases costs, and creates panic. With a dynamic plume model, you can create and share up-to-the-minute reports with stakeholders to ensure everyone has the information they need to respond swiftly and safely.
How else can I use dynamic plume modeling software outside of emergency response scenarios?
Dynamic plume modeling software like SAFER One can help you investigate odor complaints more efficiently by showing exactly where an odor is coming from—whether it's your plant or a neighboring one. You can generate automatic reports and share them with the community or local agencies to show the odor source and outcome.
You can also use dynamic plume models to train and prepare for specific emergencies that may impact your operations. By running through scenarios ahead of time, you can ensure teams know the right course of action to take should an actual incident occur.